In the world of digital investigations, precision and integrity are paramount. As cybercrime grows more sophisticated and the volume of digital evidence continues to expand, the need for reliable and accurate computer forensics has never been more critical. Precision-driven computer forensics plays a central role in ensuring the integrity of every digital investigation, providing law enforcement, corporations, and legal teams with the tools needed to uncover and present evidence that stands up to scrutiny in the court of law. Computer forensics is the process of collecting, preserving, analyzing, and presenting digital evidence in a way that ensures its authenticity and integrity. Whether investigating data breaches, fraud, cyberattacks, or intellectual property theft, the meticulous nature of forensic procedures is essential for maintaining the validity of evidence. Precision-driven methods ensure that investigators follow established protocols, preserving the chain of custody and guaranteeing that data is unaltered and admissible in legal proceedings.
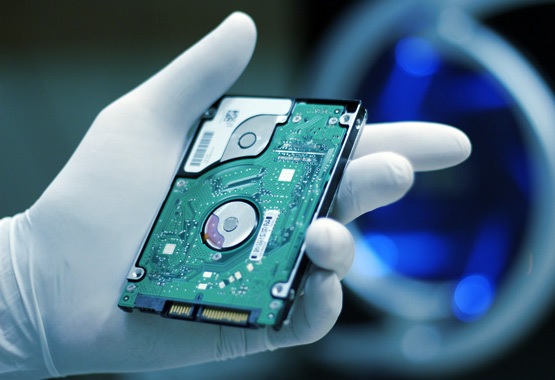
One of the core tenets of precision in computer forensics is the application of industry-standard tools and techniques. Forensic experts use specialized software and hardware to examine digital devices such as computers, smartphones, and servers. These tools are designed to recover deleted files, track digital footprints, and uncover hidden data without modifying or damaging the original evidence. Whether it is recovering emails from a corrupted hard drive or analyzing metadata from a digital photograph, precision-driven techniques enable experts to extract critical information with absolute accuracy. Another key aspect of precision-driven computer forensics is the process of data preservation. In the digital world, evidence can easily be tampered with, erased, or altered. Therefore, forensic experts must employ techniques such as disk imaging to create exact copies of digital devices, preserving all data in its original state. This ensures that investigators can work with replicas of the evidence, preventing any risk of contamination while still enabling a thorough analysis. The integrity of the original data remains intact, which is crucial for upholding the credibility of the investigation.
Detailed logs and reports track every step of the investigation, including the methods used to extract and analyze evidence. This documentation serves as a record of the investigation, proving that the forensic process was conducted with integrity and accuracy. In legal proceedings, this documentation can be pivotal in demonstrating the reliability of the evidence and the professionalism of the investigators. Additionally, precision-driven forensics involves not just the collection and analysis of data, but also the careful interpretation of that data. Digital evidence must be understood in context whether it is identifying patterns in network traffic or deciphering encrypted communications. Computer Forensics Guide uses their knowledge of both technology and law to ensure that their findings are clear, relevant, and meaningful in relation to the case at hand. Ultimately, the role of precision in computer forensics is about trust. By maintaining the highest standards of accuracy and integrity in every stage of the investigative process, forensic experts ensure that their findings are credible, trustworthy, and admissible, enabling the fair and just resolution of digital crimes.



